Hi Team,
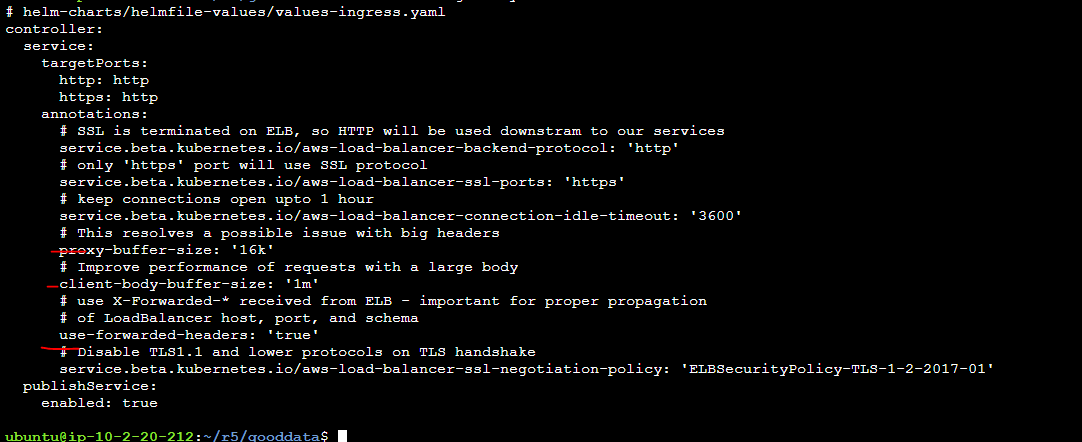
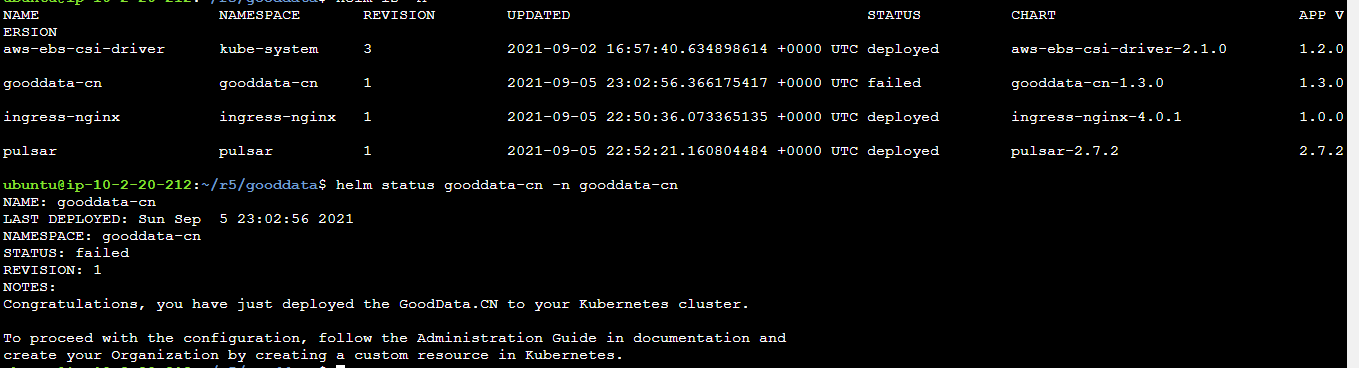
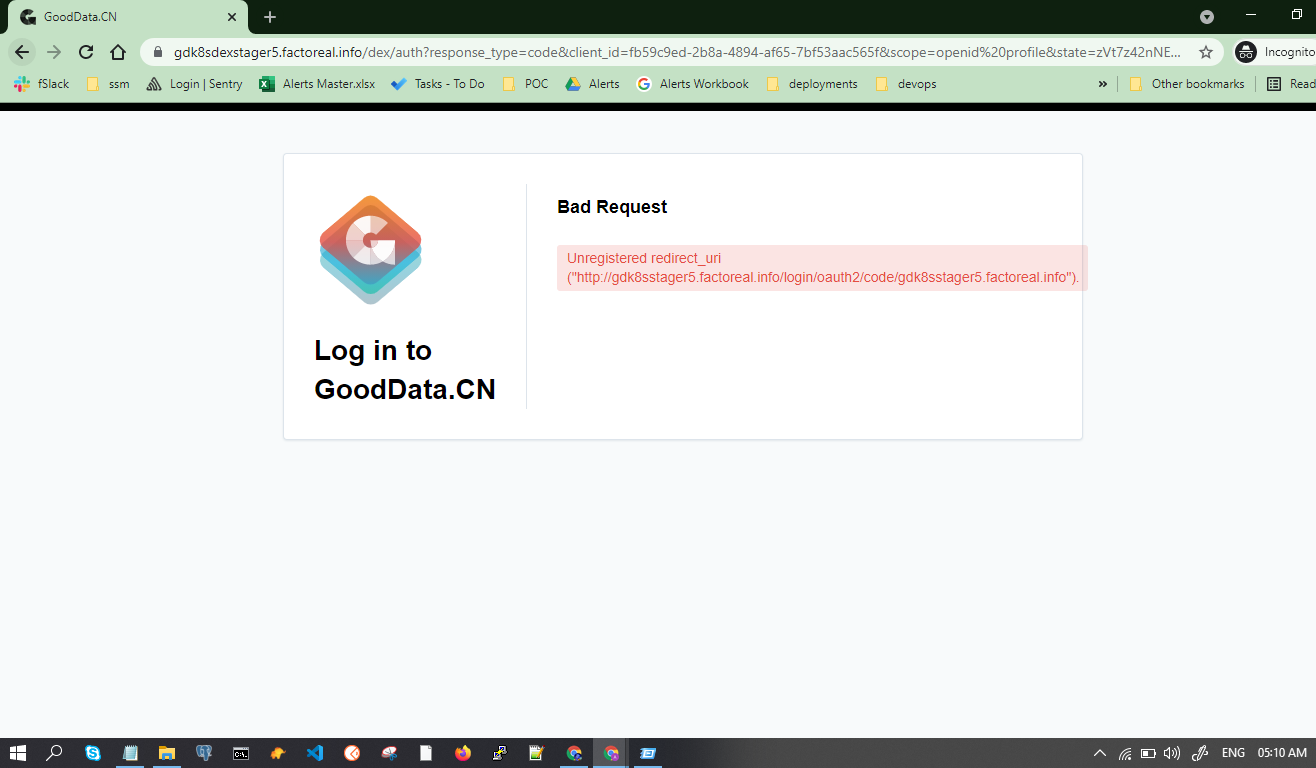
We have deployed the GD.CN with DEX after sucessfull installation we are able to bootstrap users,workspaces via cli . However UI login screen throwing the bad request
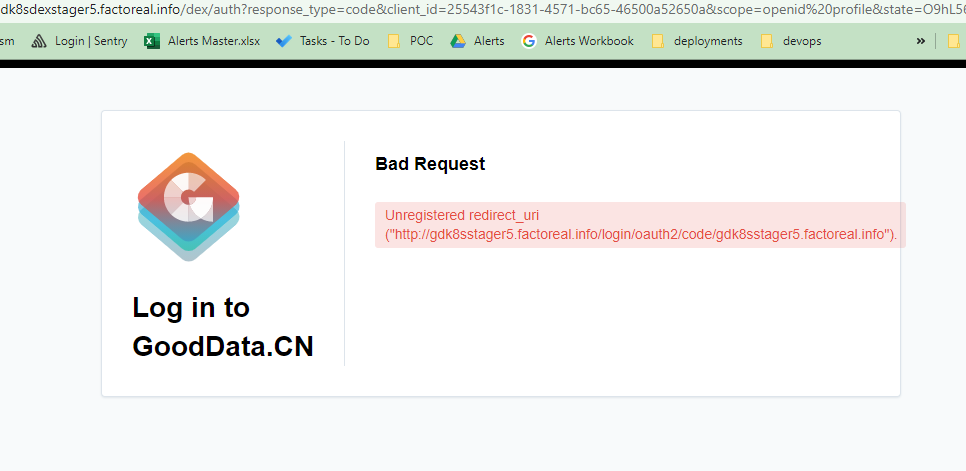
Kindly help us how to fix / add callbacks !
Ref:
https://www.gooddata.com/developers/cloud-native/doc/1.3/administration/auth/
https://www.gooddata.com/developers/cloud-native/doc/1.3/administration/auth/built-in-oidc/
Regards,
Ashok
Best answer by Robert Moucha
View original